OSINT Insider Issue #8 - Exploring a Secret Underground OSINT Marketplace
In this edition of the OSINT Insider, we will expose the criminal side of a new OSINT Marketplace and introduce a new section covering the illicit OSINT community.
In this edition of the OSINT Insider, we will expose the sale of breaches and IntelX keys on a new secret OSINT Marketplace, introduce a new regular section covering illicit OSINT tools that provide access to privileged information, discuss a UK Lookup tool that provides access to sensitive financial information, and look at new unique data sources, including an EU Public Database, a tool that allows you to see whether you’ve been searched on Flock, and an illicit tool that still seems to have access to protected CNAM records.
The free version of this edition will cover:
Flock Surveillance Images Are Now Public Records, An Exciting Precedent for OSINT Investigations
Caller ID APIs Are Down and No Longer Available in The US and Canada As The Governments Restrict Access to Personal Information
OSINT Industries Introduces New Advanced Filters, Making Search More Precise and Less Time-Consuming
This full edition includes the new Com Corner section (more on that below) and covers the points mentioned above, as well as:
Marketplace Expose, Including Illicit/Cybercrime Infostealer Data Lookup Services, IntelX Keys, Custom Modules, and Breaches for Sale
GEOINT Tool that Returns More Accurate Results than Picarta API
Up-to-date Country-Specific OSINT Resource Toolkits: Osint-for-Countries-V2.0 and Unishka
New Tool For Private Investigators in the Field that Addresses Common Issues
Telegram Tool that Decodes Messages Where a User Used the Spoiler Feature
Tool that Analyzes ALPR Camera Coverage in the USA by County
FOIA Request Library for France
EU Public Database that Allows You To Potentially Correlate Discord User IDs with SORs Reports Associated with Them
GitHub Repo that Provides Historical Records of China-Based X Accounts
Skyfall-GS – the Latest Example of a Fascinating Rendering Technique Using 3D Gaussian Splatting
New Tool that Shows Whether and Who Has Searched Your License Plate on Flock
New PimEyes AI Report Implementation that Provides Surface-level Results
New Tool that Can Soon Rival Human-Written Reports, and which Aids in OSINT Collection
r00m101 Reddit Tool Added New Exciting Features and Now Has a New Name!
SIGINT Tool that Allows You to Track Vehicles Transmitting APRS in Real Time
New Tool for Name Lookups on Breach Forums
New Tool that Enables Centralized Search Across Social Communities on Multiple Platforms
Introducing the Com Corner:
The goal of The OSINT Insider is to keep you updated on everything happening in the world of OSINT, both good and bad. Unfortunately, there is a lot going on in the illicit world, which is why we are announcing the addition of a new regular section to The OSINT Insider - The Com Corner. This section will report on The OSINT Com and the tools its members use.
The Com Corner will discuss unethical OSINT tools and offer a glimpse into the toolbox of a member of The Com. Celebrities and high-profile OSINT investigators are often targeted for swatting, SIM swapping, EDRs, and doxxing - cybercrimes frequently facilitated by this notorious online community. By shedding light on this dark side of OSINT and The Com’s modus operandi, we aim to raise awareness of these risks and help individuals better protect themselves and their privacy from threats such as EDRs, SIM swapping, unauthorized access to regulated data, etc. By developing a deeper understanding of The Com’s culture and methods, professionals will be better equipped to recognize the threat and respond effectively.
The Com Corner section in this edition will cover the following topics. Please note that the unredacted tool names are available in the paid portion of the newsletter:
[Redacted Tool Name] Receives a Subpoena, [Redacted Tool Name] Also Claims To Be Potentially Targeted by The FBI
[Redacted Tool Name] Tries to Become a White Hat Tool, Goes Terribly
A New Alternative to [Redacted Tool Name]?
[Redacted Tool Name] – Another Infostealer Tool Providing Access to Passwords and Cookies
Com Data Provider That Claims To Be Superior To [Redacted Tool Name]
[Redacted Tool Name] Grows Its Empire With The Acquisition [Redacted Tool Name]
Discord Lookup Tool that Utilizes DSA Sanction Data
US Lookup Service Launched by [Redacted Tool Name] that Sources Data From The Credit Industry and Retrieves Information About Employment, Debts, etc.
Com OSINT Tools that Potentially Enable Cybercrime, Including Potentially GLBA-Violating US Lookup Service, TLO, and CNAM Tools
Com Tool with a Nazi Owner Openly Advertised for Swatting
UK Lookup Tool that Contains Rare PII Data, Including Regulated Bank Account and Credit Information
Potential Competitor to [Redacted Tool Name]
Important Announcement About the Future of the OSINT Insider:
You may have noticed this edition took a long time to come out. This is because the only person working on this newsletter up until now (Aidan Raney) cannot sustain the amount of work needed to produce it on a consistent and timely basis. Preparing the newsletter in its current form and scope requires hundreds of hours of labor, its quite a bit more than just writing. We test new tools, investigate data sources, and monitor hundreds of sources to find anything important to our readers, so you don’t have to. We monitor nearly every newsletter, social media account, subreddit, Discord server, Telegram channel, blog, etc related to OSINT. One person doing this in their free time simply isn’t enough to sustain this level of work anymore, especially on a monthly release cadence.
If the newsletter is to continue to exist and have a consistent cadence, we need part-time staff or freelancers to assist, but currently, the newsletter does not make enough to sustain such expenses. Because of this, while the newsletter is unlikely to go away completely, if we cannot secure enough paid subscribers, the newsletter’s scope will likely have to decrease significantly to reduce the amount of labor required while maintaining the cadence that we originally promised (once per month). This edition contains over 30 topics, with in-depth research on every single one; that level of depth simply isn’t sustainable without additional help.
While we would love to continue freely sharing all of the amazing research we do, as we did in the previous edition, because each edition requires a significant amount of labor, moving forward, access to the full edition will be available to paid subscribers only. Free subscribers can still access a handful of free posts in the free section of each edition, and Substack offers a free one-time copy of the paid edition if you are unsure of whether it’s worth it.
We’ve also added a founding subscriber plan for readers who can afford to support the newsletter in a more significant way. A few people have already subscribed to this plan, and we can’t thank them enough. It’s subscribers like these and their generous support that will keep this newsletter running for a long time.
Free subscribers can claim a one-time free trial copy of this edition, courtesy of the OSINT Insider, or upgrade their subscription to The OSINT Insider at the end of this free section. If you aren’t already subscribed, please do so:
Previous Edition:
In the previous edition of the OSINT Insider, we dived deep into the world of underground OSINT, introducing tools that scrape dating apps and Discord to assist with cold cases and infidelity investigations, and exploring alternatives to the O’Reilly API. We also discussed the usefulness of OSINT tools for tackling human trafficking and looked at changes coming to the US OSINT Community. Read more here.
OSINT News
📌 Flock Surveillance Images Are Now Public Records, An Exciting Precedent for OSINT Investigations
In November 2025, a judge in Washington ruled that images taken by Flock’s automated license plate reader (ALPR) cameras, located in cities such as Stanwood and Sedro-Wooley, qualify as public records under Washington’s Public Records Act and should not be exempt from disclosure upon request.
The fact that time- and location-stamped images of cars captured by ALPR cameras can be requested through standard public records requests means that these photos can be used to track a vehicle’s movements and identify the location where it was last seen, which is likely to prove useful for vehicle OSINT investigations within Washington’s jurisdiction.
📌 Caller ID APIs Are Down and No Longer Available in The US and Canada As The Governments Restrict Access to Personal Information
CNAM data, which websites such as Seven and CallerIdtest used to provide when querying unknown numbers, has been reported to be inaccessible. SS7 is a set of telecommunication signaling protocols used by phone networks to establish and manage calls and messaging services, and before the access to it was restricted, OSINT investigators could use SS7 signaling data to retrieve caller name information tied to an unknowing number sourced from CNAM records. However, now even large companies are restricted in their access to personal information through CNAM records. In fact, CallerIdtest is now shut down, which they claim is related to the restrictions introduced by the Daniel Anderl Judicial Security and Privacy Act, commonly known as “Daniel’s Law,” which aims to protect the personal information of certain New Jersey public officials, including phone numbers, from public disclosure.
A similar process is happening in Canada, where the Canadian Local Number Portability Consortium (CLNPC) has tightened rules around caller ID lookups and prohibited the use of NPAC data for “publicly available telephone lookup services.” To access Canadian NPAC databases, non-members have to apply for authorized access, demonstrate a legitimate need, and show that they will be seeking consent from end recipients as part of their service.
Advertisement/Promotion
infostealers.info
🔗 URL: https://infostealers.info/invite/712CAE1F
🛡️ Defanged: [https://infostealers[.]info/invite/712CAE1F]
Summary: Infostealer data is the new breach data, billions of records publicly accessible online to anyone with internet access. Just like breached data, the data was originally sourced by malicious actors, who then leaked it online, making it accessible to anyone with an internet connection, providing an opportunity for investigators to responsibly use this data for their investigations.
And unlike breach data, which only reveals a single record from a single company, infostealer data is a person’s entire digital footprint directly from their browser. Every website they saved a password to, the URL of every website that stored a cookie on their device, the names of their files and folders, their saved payment methods, autofill data, cryptocurrency wallet information, etc., it’s a treasure trove for investigators working any sort of case.
Since this data is so powerful, it makes sense to implement a $1 search for infostealer data on every email address or phone number tied to your subject/case. Those few dollars of searches per case could be the difference between cracking a case with extensive digital footprint information and not finding anything useful at all. The potential for legitimate investigative use cases is truly unlimited with this new data source.
Sign up for infostealers.info today and get 3 free demo searches before committing to purchasing credits and completing our KYC process.
Data Available:
Saved passwords and logins from the browsers of over 50 million devices around the world (also contains the URL the password was saved to, providing a powerful digital footprint), over 20 billion records in total
Autofill data (Can include information like full name, billing addresses, shipping addresses, contact information, or anything else someone might save to their browser)
Search By:
Phone Number
Email Address
Username
Domain
Password
Any Keyword - Name, Address, etc (Mostly restricted to autofill data searches)
COMP ID (Gets all of the data from a specific device)
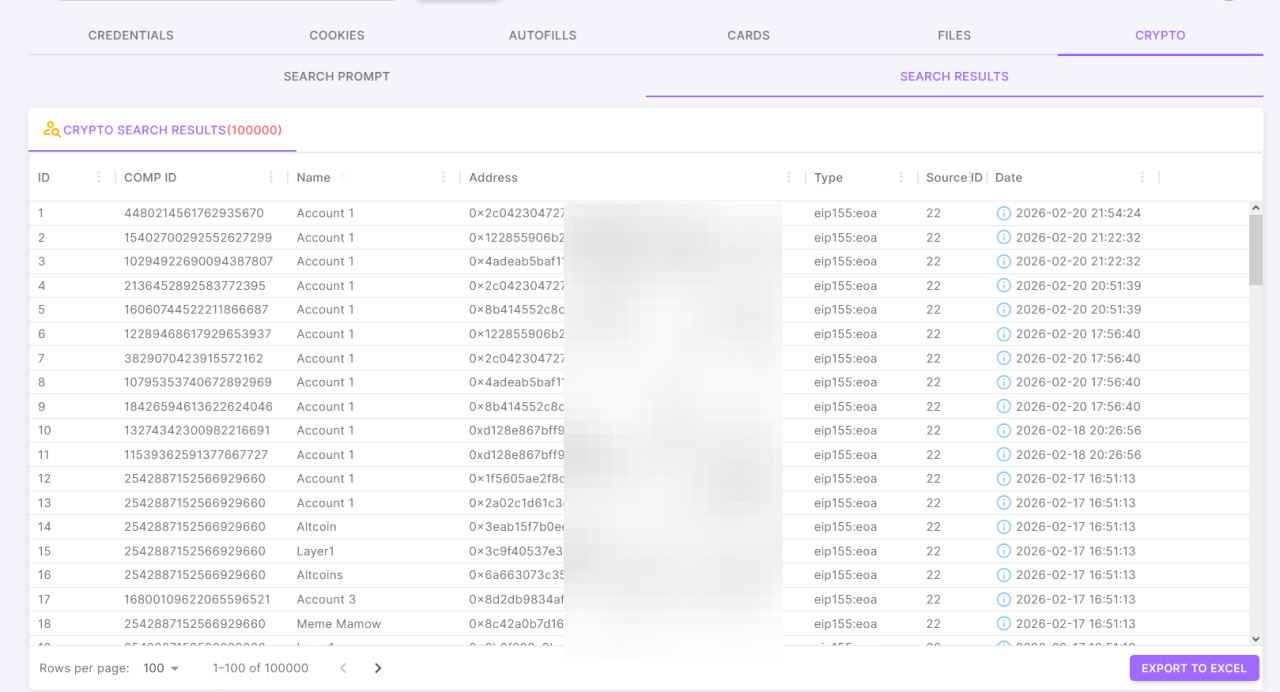
NEW - Crypto Currency Address (Only available in the full platform) - Only Solana and ERC20 addresses are supported currently.
Cost/Access:
$1 per credit (bulk discounts available), ~1-5 credits used per search, depending on the type
All accounts are required to pass a KYC check before being able to purchase credits.
Non-pro accounts will have a censored password field everywhere, the login field will be partially censored in domain search results, and the autofill values will be completely censored.
$200 per year for Pro access to get all results, including the censored results.
Other Important Details:
It’s recommended to use infostealer data as a starting point and then perform parallel reconstruction efforts, as this data may not be admissible in court under the fruit of the poison tree doctrine.
The full platform provides additional data from infostealer logs, such as stored cookies (acts as a pseudo browsing history), autofill data (can include addresses), saved payment methods (credit cards), system information (file tree), and cryptocurrency wallets (trace hidden assets or unmask anonymous crypto users).
You can also export the raw contents of the logs with the full platform. Raw logs contain information vital for incident response (exact time of infection, device hostname, IP address, directory of infection, etc), and even more data useful for investigations like actual browsing history, desktop screenshots, installed programs, network information, installed crypto wallet information, and more.
In the full platform, you can also perform much more advanced searches, including keyword searches (with boolean and wildcard support), searches against URLs, file/folder names, crypto addresses/wallets, and any other field we index in our database! Go here to learn more about the full platform, and reach out for a free demo + trial: https://www.alerts.bar/
Sign up to get 3 free demo search credits to test out the product!
Law enforcement working in ICAC (internet crimes against children) units can reach out for free access at: info@alerts.bar, Please Title Your Email “ICAC Law Enforcement Access” and CC: aidan@alertsbar.net
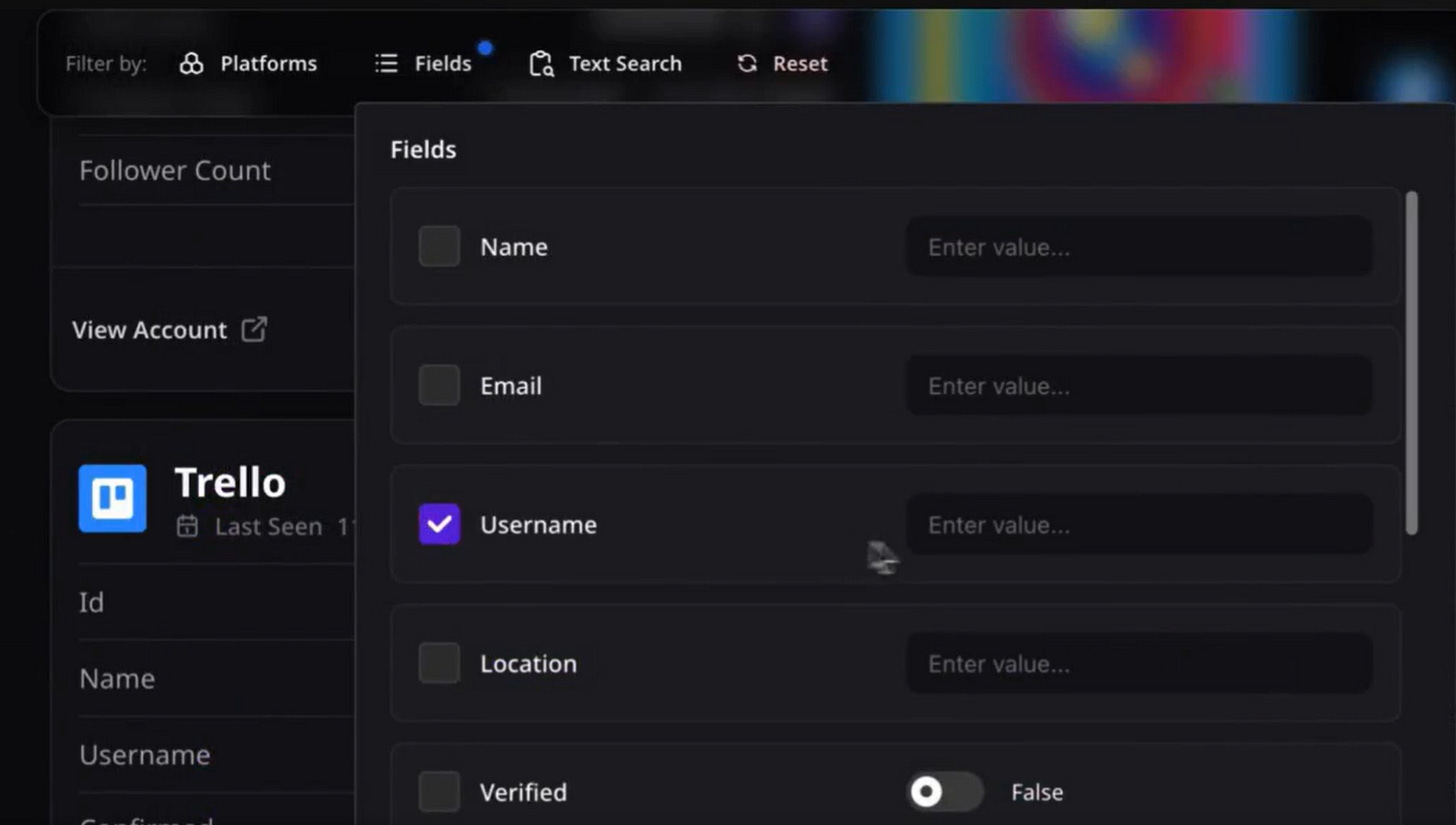
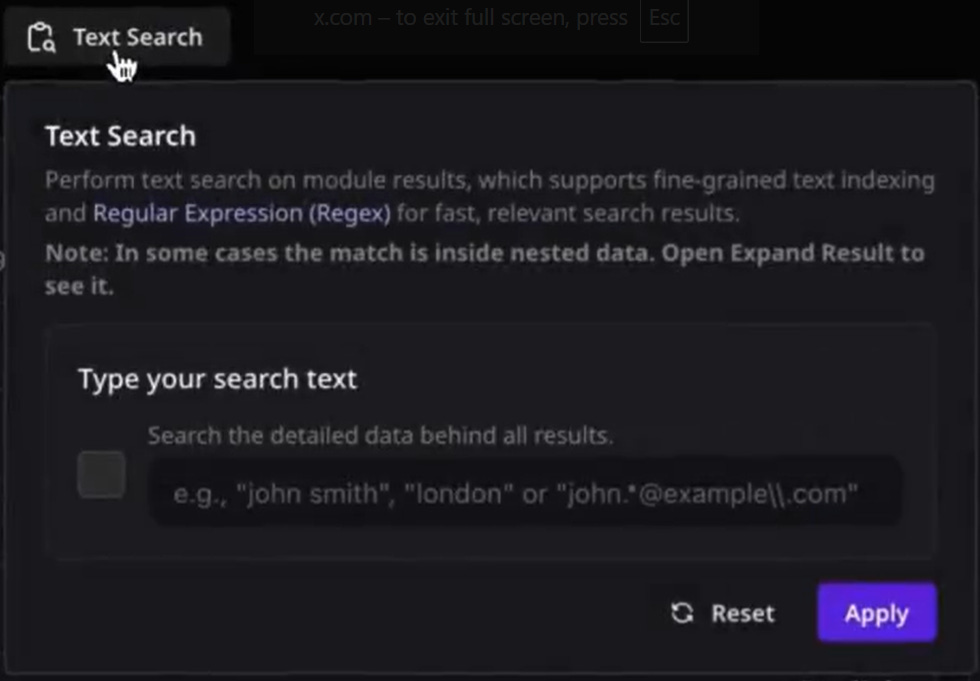
📌 OSINT Industries Introduces New Advanced Filters, Making Search More Precise and Less Time-Consuming
OSINT Industries added advanced filters that allow investigators to run text searches, search by modules and specific fields, e.g., name, platforms, as well as to combine and reset the applied filters more easily. This makes the search for information more effective and less time-consuming.
These features also make sorting through less relevant search results much more efficient, as the process is automated, improving link analysis.
Watch a video showing how to apply the filters by following the link:
https://x.com/OSINTindustries/status/1994451224855294302?s=20
Because each issue requires substantial time for in-depth research, analysis, and writing, the rest of this post is now available to paid subscribers only: