OSINT Insider Issue #9 - Australian Broadband APIs Leak Subscriber Info, Untapped Facial Recognition Tool, and New OPSEC Risks
In this edition of the OSINT Insider, we cover a relatively unheard-of facial recognition tool that produces exceptional results at affordable prices, assess a new Australian OSINT method, and more!
In this edition of the OSINT Insider, we will look at an OSINT company that provides more accurate results than FaceCheck or Pimeyes, ways in which the Com can bypass KYC security checks, and discuss a way to scrape subscriber information held by an Australian broadband provider. Additionally, we will cover ways in which investigators can find out more information on a shell company, even when they encounter a registered agent and new OPSEC risks.
The free version of this edition will cover:
OSINT Industries Launched a Massive Spring Update to Improve Workflow
Discord.id says “Screw Them Anyway” When Discord Takes Action Against it
Impressive Facial Recognition Tool that Detects Faces in Obscure Images And Returns More Results Than FaceCheck or Pimeyes
Sending Instagram URLs Can Compromise Your Anonymity and OPSEC
How Subscriber Information Held by an Australian Government-Owned Broadband Provider Could Be Scrapped
Because each issue requires a significant amount of time and effort for research and writing, access to the full edition is available to paid subscribers only.
The full edition includes The Com Corner section and covers the points mentioned above, as well as:
A Major OPSEC Alert Regarding Tile – The App That Potentially Facilitates Stalking by Compromising Your Geolocation Data
New SOCMINT Video Search Engine for Different Platforms
Ways to Pivot When You Find a Shell Company or Registered Agent in Company or Individual Due Diligence
Tool that Grants Access to a Database of Every Politician Worldwide
New Rival to Holehe and a Free OSINT Industries Alternative
A New GPSjam Alternative that Allows to Detect GPS Interferences in Real Time
Bellingcat’s New Flight Tracking Tool that Uncovers Important Patterns in Flight Data
New Historical Database of Various Cybercrime Forum Usernames
New TikTok Comment History and Keyword Search Tools with Effective Filters and Massive Databases of Archived Content
ACLED Launches ACLED Trends – a Tool that Helps to Anticipate Political Instability Worldwide Before Violence Erupts
Database on Armed Conflict, Civil War, and Organized Violence with Global Coverage
Tool that Allows to Identify Vulnerable Access Point Devices Worldwide
New Metadata Extraction and Geolocation Analysis Tool With an Impressive Investigation Potential
India Document Search Engine that Provides Access to Court Documents
Google Fact Check Tools that Support Search in Multiple Languages
Automated Dorking Tool that Scrapes File URLs
New Tool that Tracks Changes in The Amount of Nighttime Light to Provide Insight into the Likely Geopolitical Situation on the Ground, to be Used in Investigative Research
The Com Corner Section looks at the following:
How The Com Bypasses KYC Security Checks
[Redacted] Announces the Addition of a Person Search and IntelX Stealer Log Export Tools and Introduces a “Legitimate” Threat Intelligence Service Which Claims to Rival Flare.io
New Illicit Tool that Provides Access to PII via Signal
Previous Edition:
In the previous edition of the OSINT Insider, we exposed the criminal side of an Illicit OSINT Marketplace and covered some of the unethical OSINT tools that provided unauthorized access to highly sensitive personal information and bank details. Specifically, we discussed a potentially Nazi-owned US lookup tool and an illicit UK lookup tool that provided rare PII data. Read more here.
OSINT News
📌 OSINT Industries Launched a Massive Spring Update to Improve Workflow
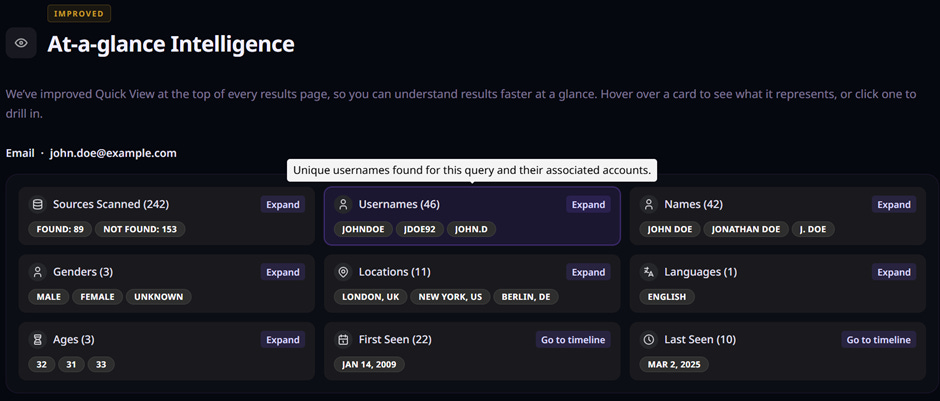
OSINT Industries expanded their At-a-glance Intelligence panel, which summarizes key results related to the digital footprint being investigated, including usernames and names, locations, first and last activity, and sources scanned. This feature aims to facilitate faster analysis of large amounts of data and deliver actionable intelligence.
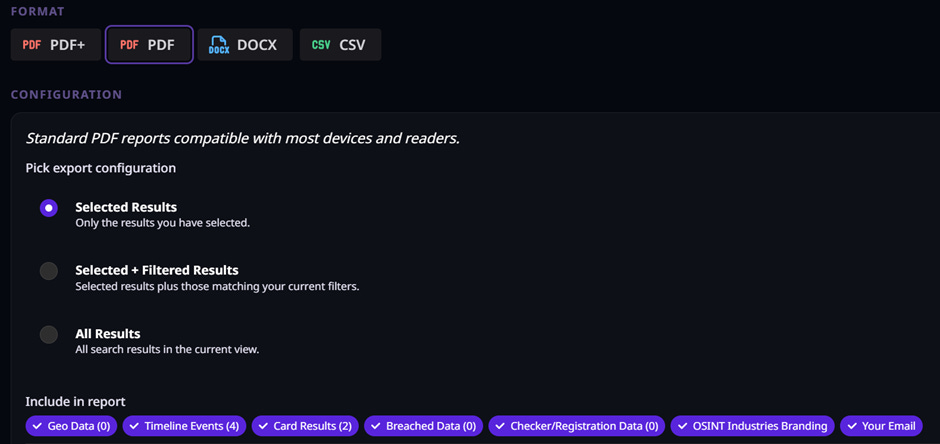
The Filter and Selection panels have also been redesigned, allowing investigators to better organize their workflow and reduce noise in their reports through the use of more advanced and targeted filters. There is now also an option to export only selected or filtered results in various formats, including PDF+, PDF, DOCX, and CSV.
Users can also take notes that are included in PDF reports, helping them organize their thoughts, leave reminders, and add relevant insights or context directly within the report.
Besides that, the Hint Composer tool has been temporarily removed from the platform because it was confusing to use, until a more intuitive alternative that is easier to work with is developed. A “Jump to Section” feature has also been added to save time when navigating through results.
📌 Discord.id says “Screw Them Anyway” When Discord Takes Action Against it
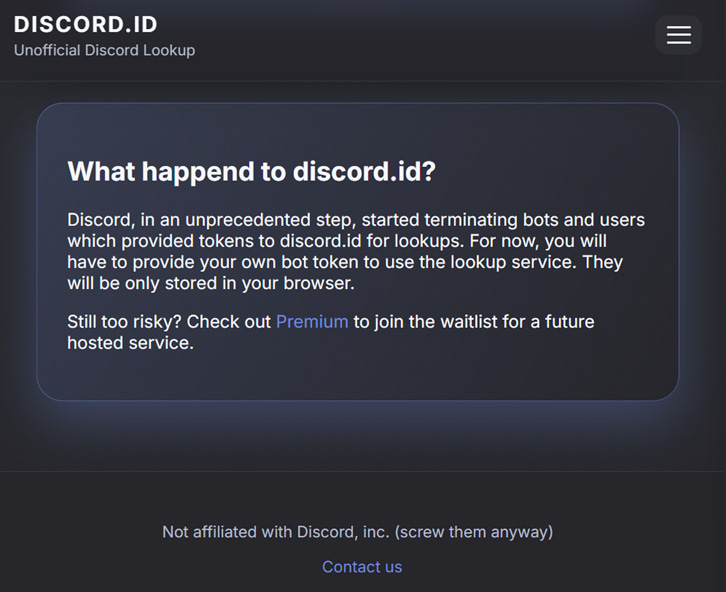
Discord is taking action against Discord.id as part of its crackdown on OSINT tools that enable unauthorized data scraping and user tracking.
Discord.id works by using a Discord user snowflake to pull the profile information on the Discord user. However, it has been announced on the tool’s website that Discord started to terminate bots and users that provided tokens to enable the lookups. This means that if the tool is used, you will need to provide your own bot tokens and store them in your browser, which is risky.
Advertisement/Promotion
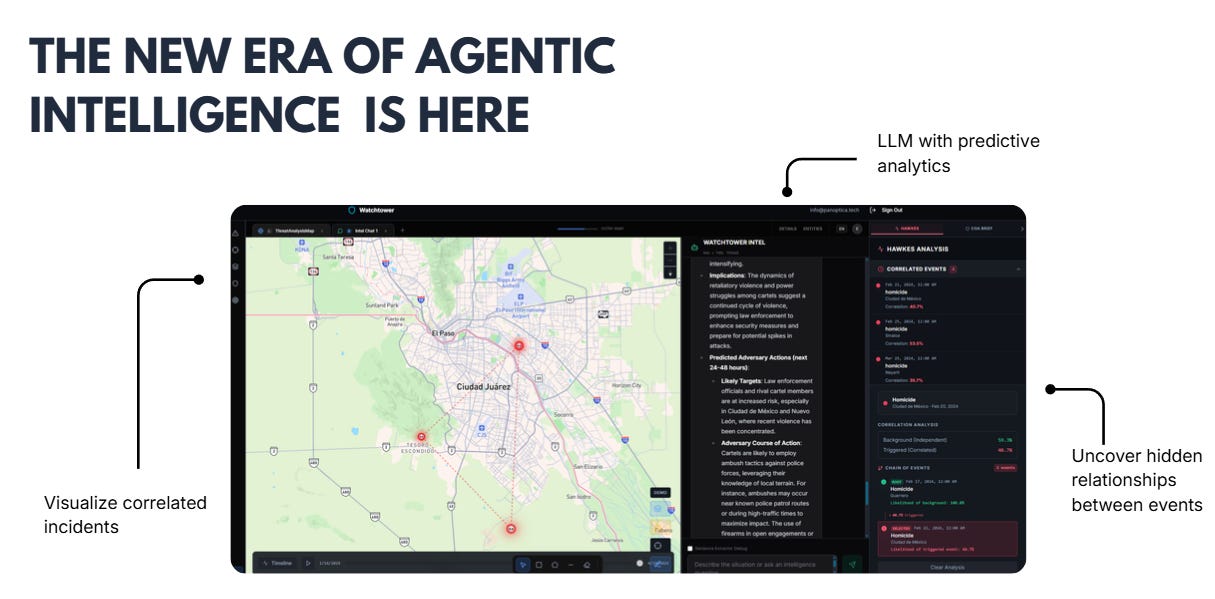
Panoptica
Panoptica Technologies, a company backed by Georgia Tech, develops autonomous agents to accelerate tactical-level intelligence and OSINT workflows by leveraging automated reasoning. The platform replaces legacy, time-consuming, and labor intensive workflows so that analysts get to do more of the things they do best: analysis. Panoptica enables organizations to identify adversary networks, forecast activity, and accelerate intelligence-driven decision making in national security and law enforcement contexts so that key stakeholders are able to make decisive decisions in high-stakes environments.
The future of agentic intelligence is here. Sign up for a free demo today
📌 Impressive Facial Recognition Tool that Detects Faces in Obscure Images And Returns More Accurate Results Than FaceCheck or Pimeyes
Eyematch.ai is a relatively unheard-of AI-driven facial recognition tool that launched a year or so ago and performs advanced face image search by comparing facial features from the uploaded photo – nose, eyes, and mouth – to detect faces online that display the most similarity to the original image. It can also detect and analyze faces even when lighting, angles, or expressions are different.
When we tested the tool, it was able to detect a matching face in obscure YouTube thumbnails and old videos. It is likely that Eyematch.ai has a much larger database of scrapped content than FaceCheck or Pimeyes, given the volume of results, as a better algorithm is unlikely to be able to produce this many additional results.
Full Disclosure: Lenso.ai is a planned sponsor for the June issue of The OSINT Insider. Given this, we had to make a decision about whether to include the following in this newsletter. However, since informing our readers about what is going on in the world of OSINT is our prime objective and integrity is a core principle of the Editor, we decided to research and include the following regardless of potential lost sponsorship revenue.
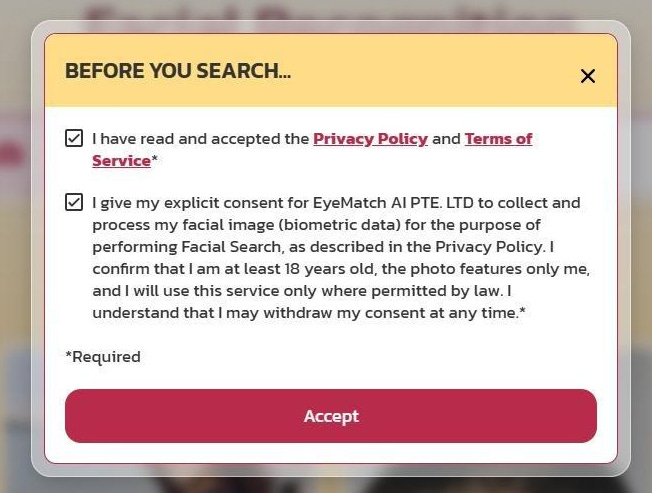
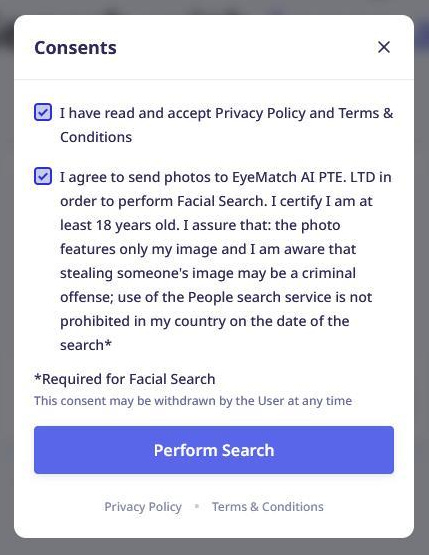
While researching Eyematch.ai we noticed that Lenso.ai appears to use its facial recognition results, which turned out to be effectively the same for the test searches that we ran for Lenso.ai and Eyematch.ai. We also discovered that in Lenso.ai’s Terms of Service they state that all people’s search results are sent to Eyematch Ltd, which is the same company as the one behind Eyematch.ai. Also, both platforms require users to give their consent to EyeMatch AI PTE.
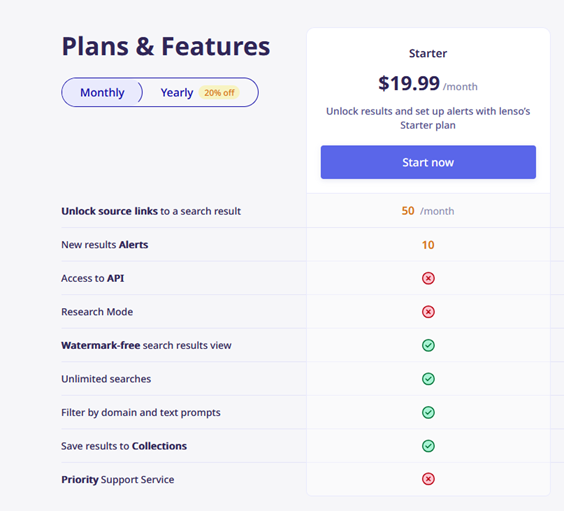
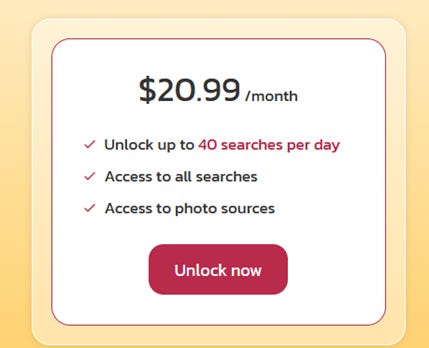
Yet, Eyematch.ai is cheaper than Lenso.ai since users get 40 searches per day on Eyematch.ai, as opposed to 50 per month on Lenso.ai.
When comparing results returned by Lenso.ai and Eyematch.ai we found that EyeMatch produces more results and includes more broad or lower confidence results, which is useful as it provides additional context to the investigation and equips the researcher with more information.
The platform allows users to identify any potential privacy or image copyright breach such as misuse of your photos and where your photos are shared, in addition to being useful for investigative professionals.
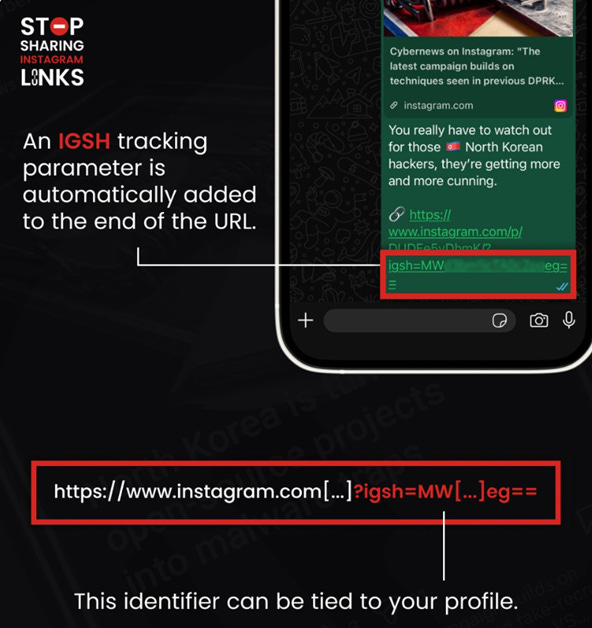
📌 Sending Instagram URLs Can Compromise Your Anonymity and OPSEC
Epieos discovered that every time you share a link to an Instagram post, an IGSH tracking parameter is automatically embedded in the URL. This identifier could be linked to your profile, which means that your account may be exposed when someone opens the link in a browser. This may compromise your OPSEC when the viewer is prompted to follow you.
For this reason, it is recommended that you remove the IGSH string at the end of the URL before sharing any links.
H/T 🎩 Epieos on LinkedIn
Advertisement/Promotion
infostealers.info
Infostealer data is the new breach data, but much worse, billions of highly sensitive credentials and records are available online to anyone with internet access. Threat actors are wreaking havoc using illicit infostealer platforms, and meanwhile most businesses that the market relies on to help catch problems like this early can’t afford the solutions needed to defend people and companies at scale from infostealers, so we produced infostealers.info, a solution for executive protection firms, pentesters, bounter hunters, auditers, and other people and businesses who take data like this and use it to protect people, investigate crimes, and prevent cybercrime, fraud, etc. The cost is low per search, and KYC is required for any access to any uncensored data to protect the data from misuse.
Sign up for infostealers.info today and get 3 free demo searches before committing to purchasing credits and completing our KYC process.
📌 How Subscriber Information Held by an Australian Government-Owned Broadband Provider Could Be Scrapped
Foilmanhacks on X (formerly Twitter) discovered a way to obtain subscriber information on broadband customers in Australia by pulling data from The National Broadband Network (NBN), which is Australia’s government-owned, open-access data network that provides broadband across the country.
Example of the data you can get:
{ “type”: “nbn”, “technology”: “Satellite”, “serviceClass”: 8, “isServiceable”: false, “newDevelopmentChargeApplies”: false, “newDevelopmentChargeAmount”: 300, “newConnectionChargeApplies”: false, “newConnectionChargeAmount”: 0, “speedPotential”: { “downloadSpeed”: 100, “uploadSpeed”: 20 }, “broadbandPlans”: [], “blacklistedAddress”: false, “lastUpdated”: “2026-03-09T10:20:22.000000Z”, “ntds”: [], “copperPairs”: [], “requiresNtdQuestion”: false, “alternateTechnology”: “”, “forecastRTC”: null, “hasFibreUpgrade”: false, “highSpeedNtdPlansAvailable”: false, “hasHighSpeedNtdUpgrade”: false, “offersSelfInstallKit”: false, “poiData”: null, “hasComplexInstall”: false } { “timestamp”:1769491595079, “servingArea”:{ “csaId”:”CSA200000010939”, “techType”:”FTTN”, “serviceType”:”Fixed line”, “serviceStatus”:”available”, “serviceCategory”:”brownfields”, “rfsMessage”:”May 2016”, “description”:”Wollongong” }, “addressDetail”:{ “id”:”LOC000188168203”, “latitude”:-34.40681139, “longitude”:150.8791513, “reasonCode”:”FTTN_CT”, “altReasonCode”:”FTTP_NA”, “techChangeStatus”:”In Design”, “programType”:”Customer-initiated N2P MDU Complex”, “targetEligibilityQuarter”:”Jun 2028”, “previousTechChangeStatus”:”Planned”, “techFlip”:”“, “serviceType”:”Fixed line”, “serviceStatus”:”available”, “mduFibreEligibility”:false, “techType”:”FTTN”, “formattedAddress”:”BLDG 67 100 NORTHFIELDS AV WOLLONGONG NSW 2500 Australia”, “address1”:”Bldg 67 100 Northfields Av”, “address2”:”Wollongong NSW 2500 Australia”, “locality”:”Wollongong”, “statusMessage”:”connected-true”, “frustrated”:false, “zeroBuildCost”:true, “speedTierAvailability”:true, “eec”:1, “coatChangeReason”:”“, “mpsid”:”2WLG-06-00-MPS-600”, “cbdpricing”:true, “ee”:true, “TC2SMD”:true } } { “timestamp”:1769491595079, “servingArea”:{ “csaId”:”CSA200000010939”, “techType”:”FTTN”, “serviceType”:”Fixed line”, “serviceStatus”:”available”, “serviceCategory”:”brownfields”, “rfsMessage”:”May 2016”, “description”:”Wollongong” }, “addressDetail”:{ “id”:”LOC000188168203”, “latitude”:-34.40681139, “longitude”:150.8791513, “reasonCode”:”FTTN_CT”, “altReasonCode”:”FTTP_NA”, “techChangeStatus”:”In Design”, “programType”:”Customer-initiated N2P MDU Complex”, “targetEligibilityQuarter”:”Jun 2028”, “previousTechChangeStatus”:”Planned”, “techFlip”:”“, “serviceType”:”Fixed line”, “serviceStatus”:”available”, “mduFibreEligibility”:false, “techType”:”FTTN”, “formattedAddress”:”BLDG 67 100 NORTHFIELDS AV WOLLONGONG NSW 2500 Australia”, “address1”:”Bldg 67 100 Northfields Av”, “address2”:”Wollongong NSW 2500 Australia”, “locality”:”Wollongong”, “statusMessage”:”connected-true”, “frustrated”:false, “zeroBuildCost”:true, “speedTierAvailability”:true, “eec”:1, “coatChangeReason”:”“, “mpsid”:”2WLG-06-00-MPS-600”, “cbdpricing”:true, “ee”:true, “TC2SMD”:true } }
Some fields include interesting details, such as ”frustrated”, which could potentially be a field to label customers who customer service representatives found were frustrated, angry, etc.
Internals of buildings might also be worth querying to see how different rooms are labeled using the LOCIDs, which could potentially reveal sensitive locations of network equipment.
For a detailed breakdown and step-by-step guide to reproducing this, please become a paid subscriber.
Because each issue requires substantial time for in-depth research, analysis, and writing, the rest of the post is available to paid subscribers only: